- Share on
-
-
-
Hand-picked related articles
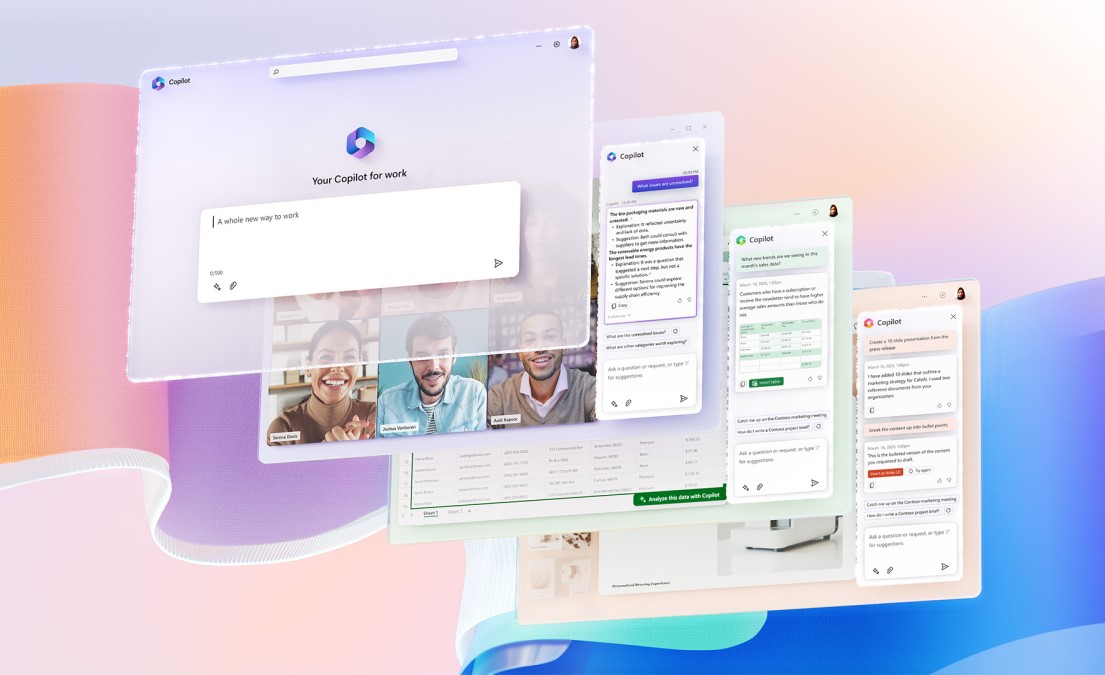
Microsoft Copilot and the Future of Managed IT Support
Today, we’re going to explore Microsoft 365 Copilot, an innovative AI-powered tool that is redefining managed IT support and the way we work. Even if you don’t work in IT, you’ll have likely seen technology like ChapGPT and Copilot being talked about in the mainstream press. As Artificial Intelligence (AI) continues to evolve, tools like… Continue reading Microsoft Copilot and the Future of Managed IT Support
- Publish date
- April 11, 2023
- Topic
- Category: Uncategorized

MDM for Apple: Protecting Your Data with Microsoft Intune and Azure Active Directory (AD)
In an era where digital transformation is fueling business growth, Apple device usage, specifically Macbooks and iPhones, has become an integral part of the enterprise ecosystem. However, as these devices permeate the business environment, concerns about data protection and unauthorized access to employee devices have risen to the forefront. This is where solutions like Microsoft… Continue reading MDM for Apple: Protecting Your Data with Microsoft Intune and Azure Active Directory (AD)
- Publish date
- July 17, 2023
- Topic
- Category: Cyber Security

Step-by-Step Guide to Activating “Find My Phone”
Whether you have an iOS, Android, or Windows device, setting up this feature can give you not just protection, but peace of mind. This guide walks you through what you need to do. Activate Find My Phone: iOS Devices (iPhone) Activate Find My Phone: Android Devices Activate Find My Phone: Windows Devices Additional Security Features… Continue reading Step-by-Step Guide to Activating “Find My Phone”
- Publish date
- August 6, 2024
- Topic
- Category: IT Support
